Introducing Living off the Orchard: Apple Script
When Built-In Features Become Security Risks: Testing AppleScript and JXA Abuse
Attackers can leverage builtin macOS tools like AppleScript and JXA (JavaScript for Automation) to access credentials, capture screenshots, and establish persistence without installing custom tools. Can your security controls detect these techniques?
Living Off the Orchard: Apple Script (LOAS) is a library of AppleScript and JXA tests mapped to the MITRE ATT&CK® framework that helps you answer that question. Security teams can use LOAS to quickly, portably, and reproducibly test their macOS environments using multiple execution methods, each generating different endpoint security logs.
Who Should Use LOAS?
🔴 Red Team - Test realistic macOS attack scenarios without custom tools.
🔵 Blue Team - Validate detection rules against real adversary techniques and build comprehensive macOS monitoring and alerting.
Why a Dedicated AppleScript Testing Framework?
While LOOBins and Atomic Red Team provides extensive macOS coverage, AppleScript and JXA deserve specialized focus.
Making LOAS a separate framework allows for:
Specialized Focus: Deep dive into macOS specific scripting nuances, TCC permissions, and application automation that would be lost in a general-purpose framework.
Multiple Execution Vectors: Each LOAS test can be executed through five different methods (CLI, script files, Swift, applets, binaries), each generating distinct detection telemetry. Adding this complexity to Atomic Red Team would be unwieldy.
Parameterized Testing: LOAS bridges the gap between documentation and testing. Unlike documentation libraries (LOLBAS, LOOBins, GTFOBins) that catalog techniques with example usage, LOAS delivers executable, parameterized tests designed for automated security validation.
Seamless Integration: LOAS uses a YAML specification similar to Atomic Red Team’s format. Conversion scripts transform LOAS tests into Atomic Red Team atomics, making integration seamless if you already use Atomic Red Team. You can also grab pre-converted LOAS data in Atomic Red Team YAML format directly from GitHub releases.
Getting Started
Ready to start testing? The easiest way is to download pre-built artifacts from GitHub releases:
# Download pre-built tests from releases
# https://github.com/cyberbuff/loas/releases/latest
# Execute your first test through any of the following methods:
osascript -e ‘short user name of (system info)’ -e ‘long user name of (system info)’
osascript get_user_using_system_info.scpt
swift get_user_using_system_info.swift
./get_user_using_system_info⚠️ Security Warning: All LOAS tests should only be run in isolated lab environments or with explicit authorization. These techniques can trigger security alerts and modify system state.
The GitHub Actions workflow automatically generates all the artifacts needed for testing. However, if you want to compile them yourself:
# Clone and setup
git clone https://github.com/cyberbuff/loas.git
cd loas
uv sync
# Validate all tests
uv run main.py validate
# Generate all test artifacts
uv run main.py build
# Execute your first test
osascript osascripts/T1033/get_user_using_system_info.scptFor detailed instructions on writing YAML tests and contributing, see the LOAS documentation.
LLM-Optimized Documentation
Ready to use with Claude, ChatGPT, or Gemini right out of the box.
Full Documentation - Complete technique descriptions and implementation details in plain text format
Individual Technique Documentation - Access specific techniques at
https://loas.dev/docs/<technique-id>.mdx(e.g.,T1005.mdx,T1087.001.mdx)
Sample Prompt:
Read https://loas.dev/llms-full.txt. I want to ask questions about the techniques.
Execution Methods
Understanding how AppleScript techniques appear in your security logs is critical for detection engineering. LOAS tests can be executed using five different methods, each creating distinct forensic artifacts and detection opportunities:
CLI (
osascript -e) - Direct command-line executionScript files (
.scpt) - Pre-saved AppleScript filesApplet (
.app) - Packaged as macOS applet bundlesSwift wrappers (
.swift) - AppleScript embedded in SwiftCompiled binaries - Standalone executables
These execution methods are documented in detail in the Red Canary Threat Detection Report. This documentation builds upon and expands their work.
Each method creates different traces in your security logs like different parent-child process relationships, file system events, and security audit logs. Understanding these variations is critical for building comprehensive detection rules.
The GitHub releases page provides all of these different files for each test.
Comparing Detection Telemetry
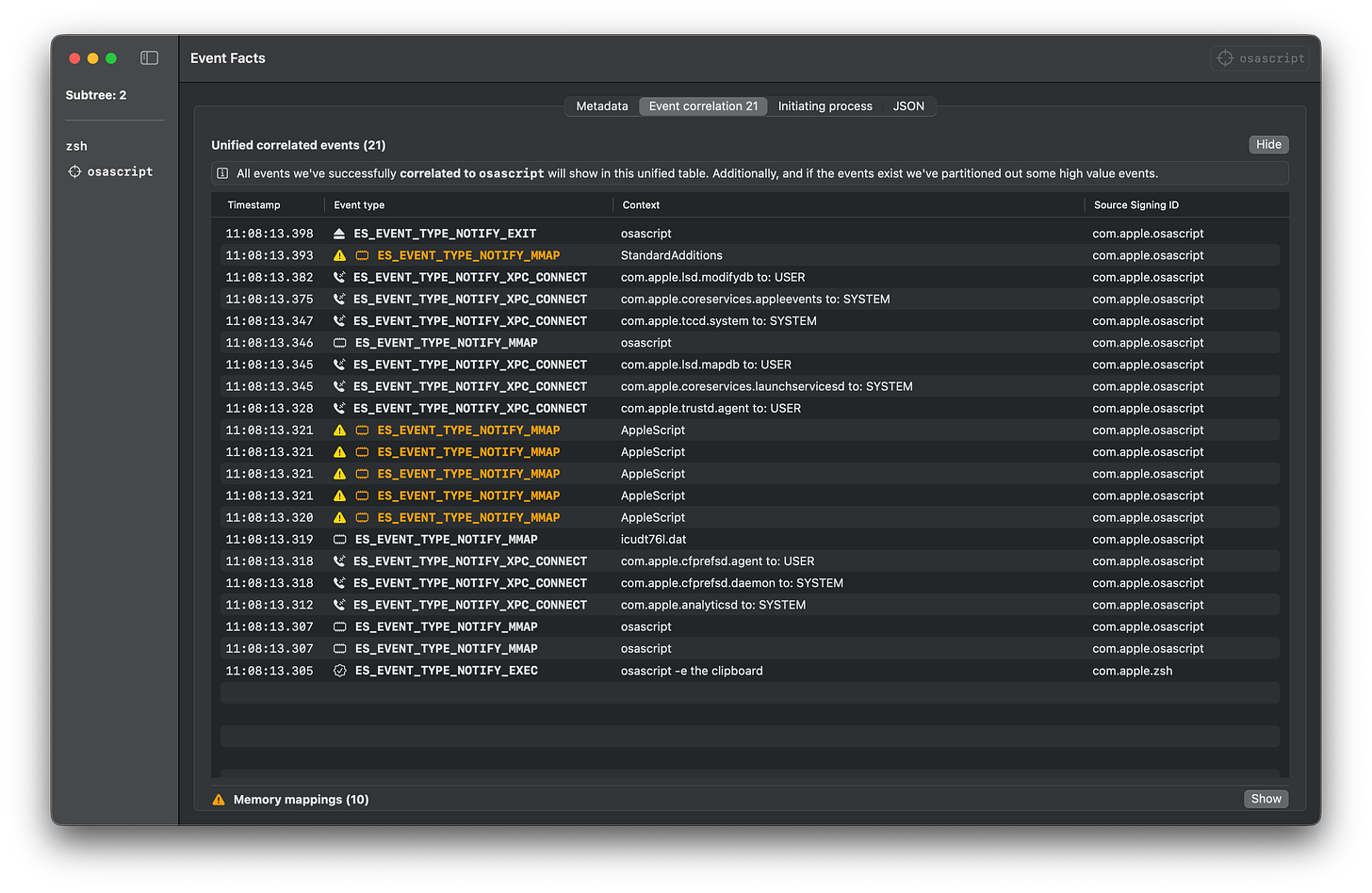
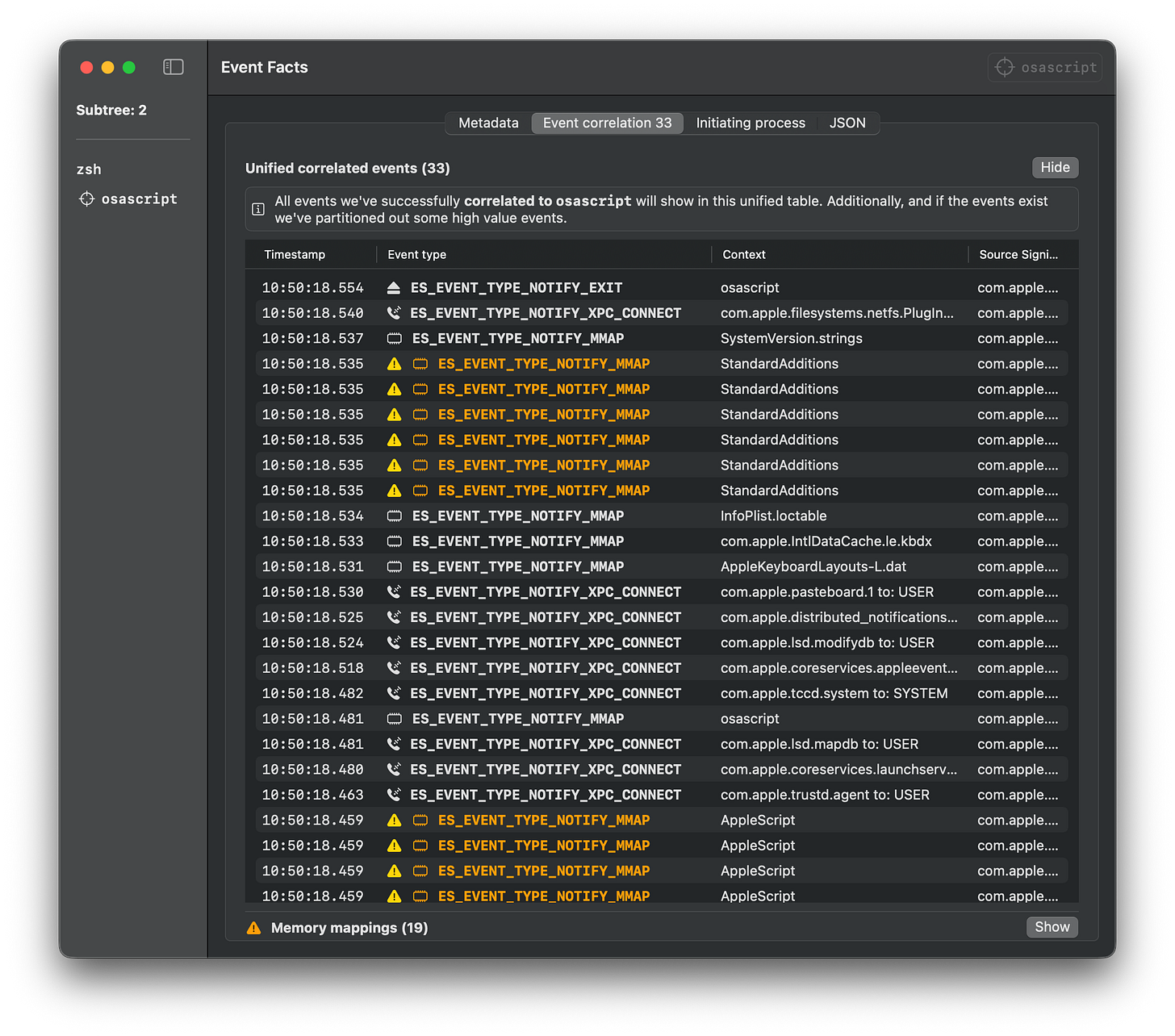
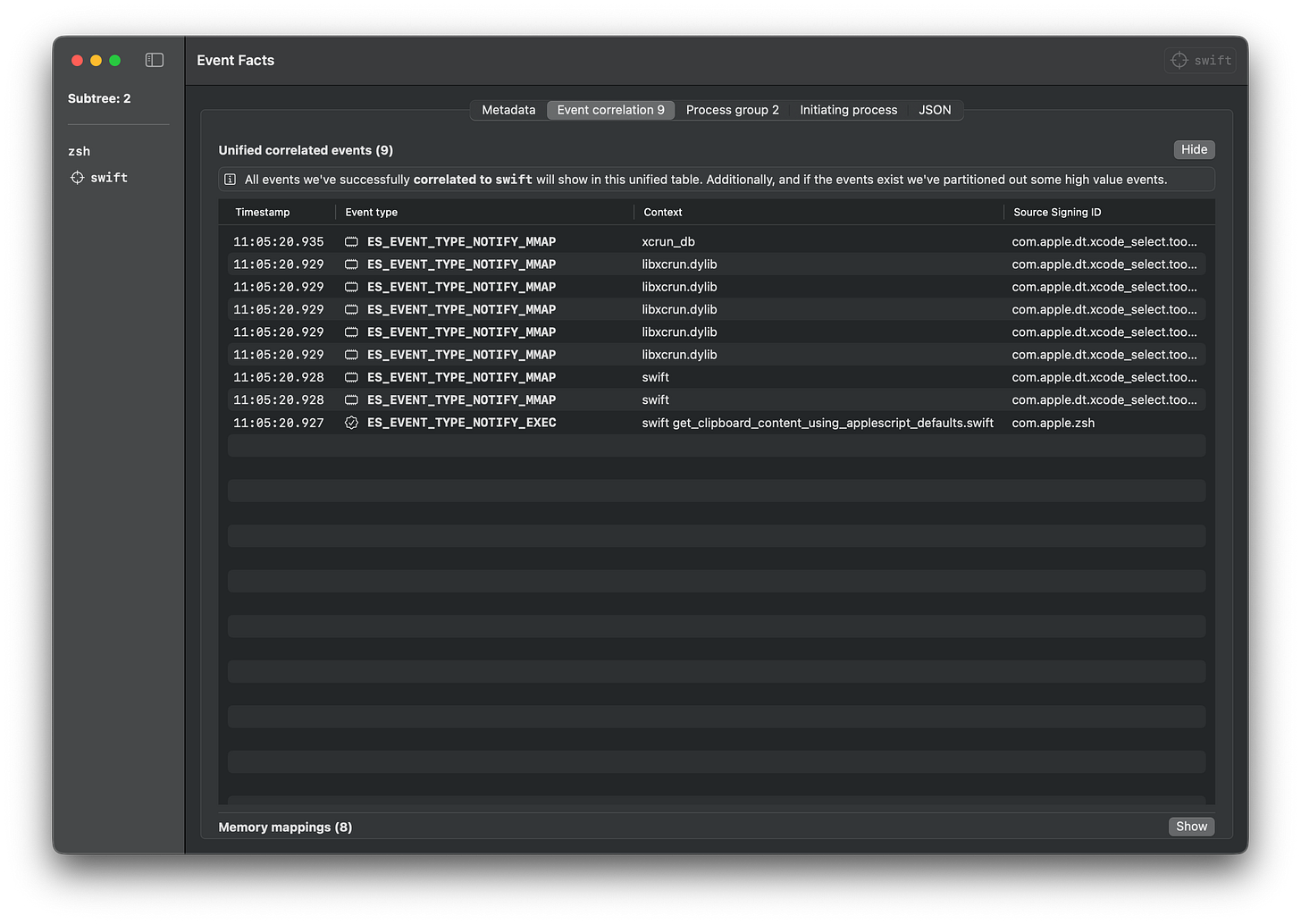
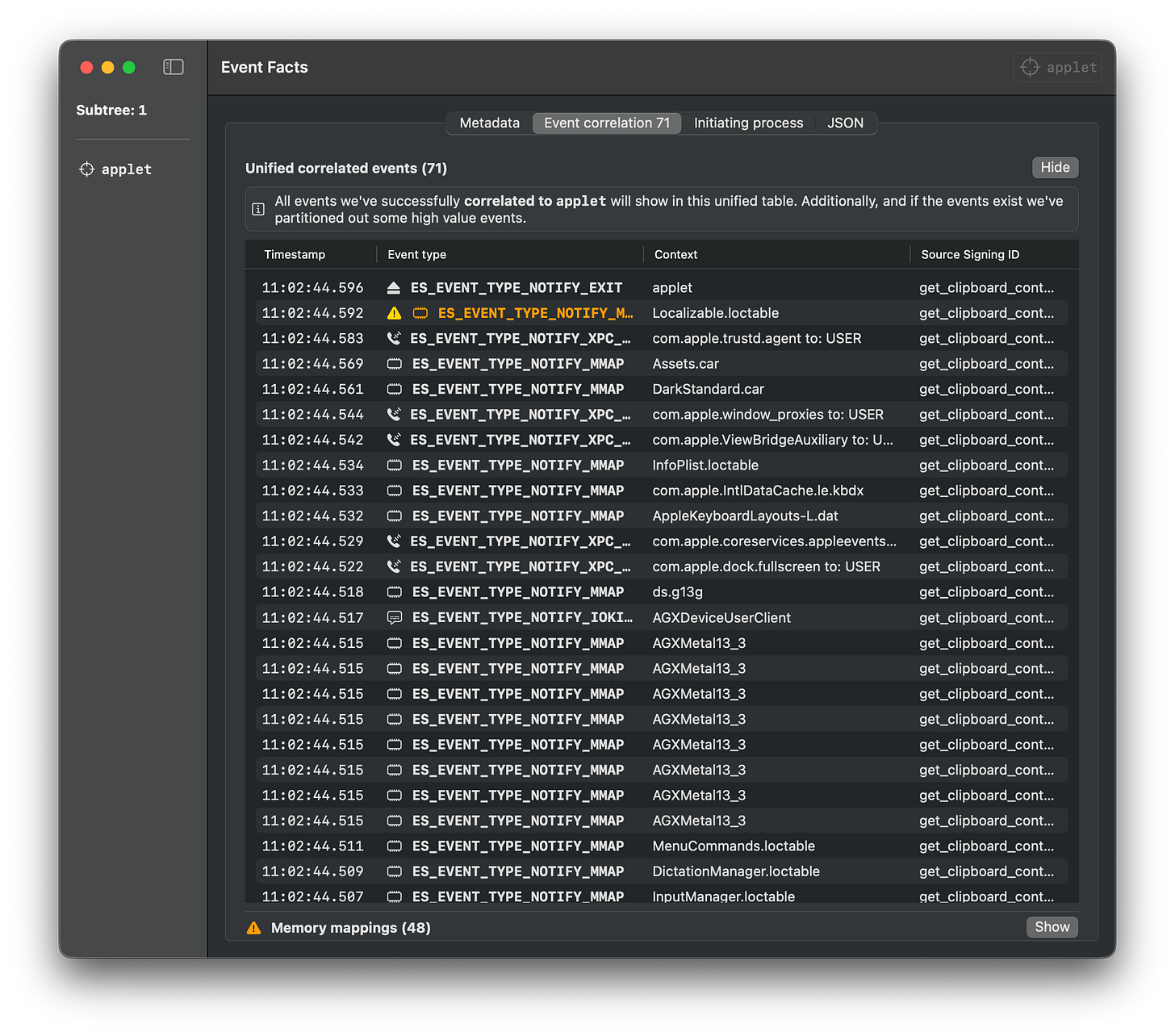
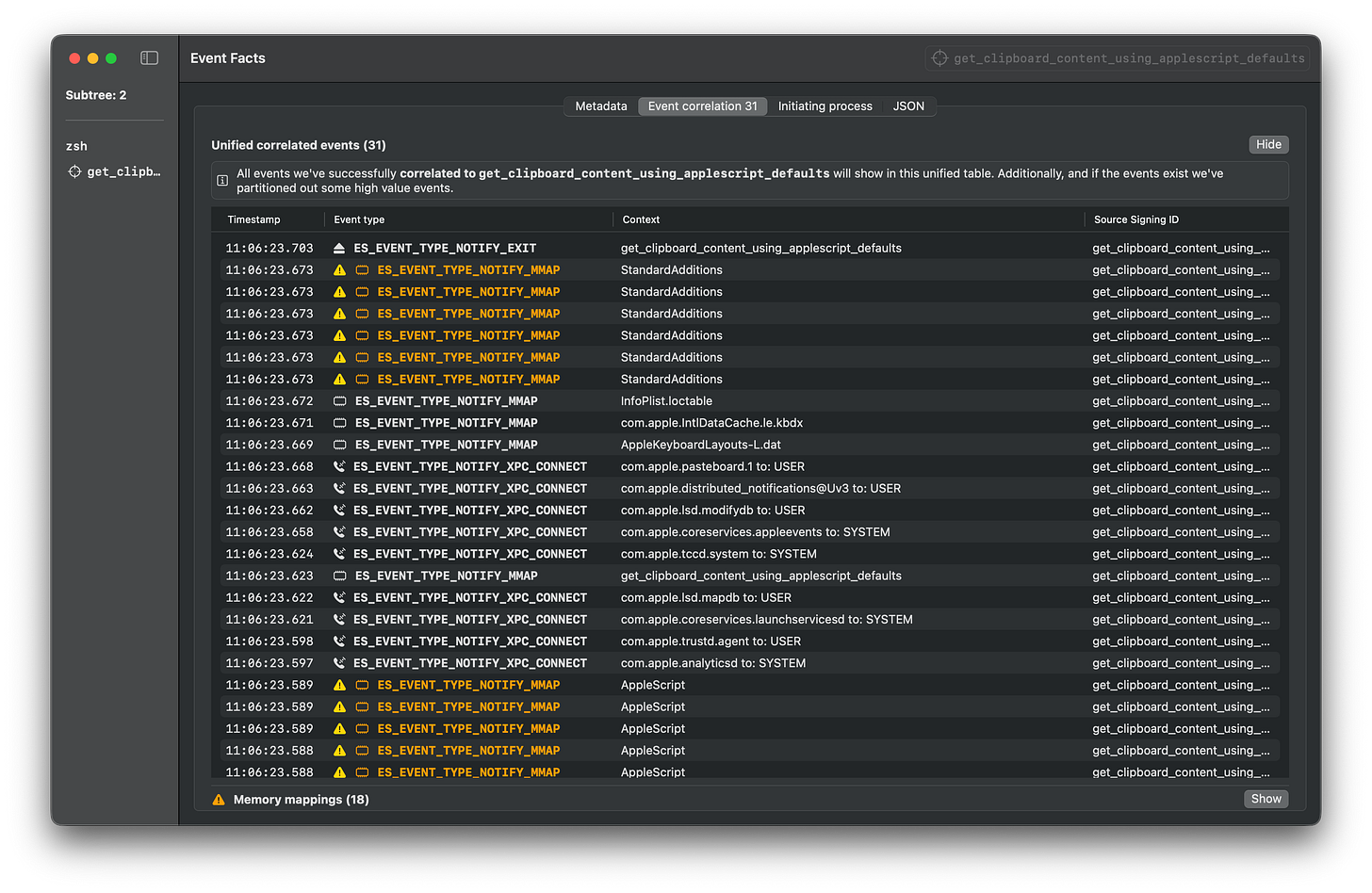
The sample Endpoint Security logs below were gathered using Mac Monitor for each execution method when retrieving clipboard content.
CLI
This is the simplest way to execute commands from this repository.
osascript -e “the clipboard”Script
Download the script from the releases page and execute it with osascript.
osascript get_clipboard_content_using_applescript_defaults.scptSwift
Download the Swift file from the releases page and execute it with Swift.
Note: You might need to install XCode Developer Tools to run Swift files.
swift get_clipboard_content_using_applescript_defaults.swiftApplet
Download the .app file from the releases page and execute it.
open -n get_clipboard_content_using_applescript_defaults.appBinary
Download the binary from the releases page and execute it.
./get_clipboard_content_using_applescript_defaultsRoadmap
LOAS is actively evolving with planned enhancements:
CI/CD Testing: GitHub Actions workflows for automated validation, ensuring atomics remain compatible as Apple deprecates and replaces APIs across macOS versions
Expanded Technique Coverage: Continuously adding atomic tests for MITRE ATT&CK® techniques beyond the current 29 implementations
Conclusion
As macOS continues to grow in enterprise environments, understanding and defending against AppleScript and JXA abuse becomes increasingly critical. LOAS provides security teams with the tools needed to:
Understand how threat actors weaponize legitimate macOS automation
Test detection coverage across multiple execution vectors
Validate security controls with MITRE ATT&CK®-mapped techniques
Improve defensive capabilities through purple team collaboration
Resources
GitHub Repository: https://github.com/cyberbuff/loas
Documentation: https://loas.dev
Latest Release: https://github.com/cyberbuff/loas/releases/latest
MITRE ATT&CK®: macOS Matrix
Atomic Red Team: https://github.com/redcanaryco/atomic-red-team
Red Canary Threat Detection Report - AppleScript: https://redcanary.com/threat-detection-report/techniques/applescript/
MITRE ATT&CK® is a registered trademark of The MITRE Corporation.
Want to contribute or have questions? Open an issue on GitHub or reach out on X @cyb3rbuff
All my content is cross posted to both cyberbuff.dev/blog and Substack. The custom blog supports hierarchical subposts with integrated table of contents, enabling readers to navigate complex topics or skip familiar sections. While Substack lacks this UI customization, it provides better subscription management and notifications. I maintain both platforms to serve different reader preferences, so use whichever suits you best.